Traditional Deletion vs. Secure File Deletion
First, it’s important to know that Windows doesn’t normally delete files permanently. “Deleted” information is only inactive on your hard drive. However, this information remains intact on your hard drive. After some time, the information can be written over. This is how traditional deletes work on most hard drives. However, this “deleted” information can be recovered easily by most recovery programs. Hackers, identity thieves, and even government officials have long since discovered that your deleted data holds a wealth of information that they may use for their benefit. To protect yourself from this potential exposure, you can do a “secure delete”, which ensures that information you wish to have permanently deleted is not recoverable.
How does secure file deletion work?
Secure file deletion works by first encrypting your data. This action turns the normal information into a scrambled code that cannot be unlocked without advanced software and knowledge of encryption. While this software is advanced, it is usually VERY easy for people to use. Multiple point encryption almost guarantee its secrecy. Next, when a user deletes their information, the deleted data remains on your drive and is eventually overwritten like other deleted data. However, if someone attempts to recover this information, it cannot be read. The final step is to overwrite the data. This naturally occurs over time, however privacy programs can speed up the secure file deletion procedure.
3 Steps in Secure File Deletion work
STEP 1: ENCRYPTION
Depending on the sensitive nature of the data, the higher encryption level you may need. Encryption refers to algorithmic schemes that encode plain text, pictures, video and all files into non-readable form or cypher thus providing privacy. The encrypted data uses a “key” to decrypt the cypher which will return it to its original form. The key is the trigger mechanism to the algorithm. So the more times you encrypt a file, the more keys will be needed to unlock the cypher. There are great free programs that will encrypt your data such as Trucrypt. However, Windows tools also offers encryption tools. Follow the direction below to encrypt your files.
How to encrypt a file or folder
- Open Windows Explorer or simply right click the file
- Right-click the file or folder that you want to encrypt, and then click Properties.
- On the General tab, click Advanced.
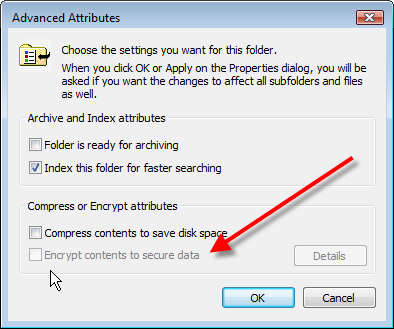
- Select the Encrypt contents to secure data check box.

STEP 2: DELETION
This is an easy step. You can simply delete the file by right clicking and clicking delete. However, you must remember where your computer has designated your deleted files to end up after deletion. You can view deleted files by opening the recycle bin.
STEP 3: OVERWRITE
Windows XP and Windows 2000 Administrators can use Cipher.exe to encrypt and decrypt data on drives that use the NTFS file system and to view the encryption status of files and folders This tool can also be used to overwrite data that you have deleted so that it cannot be recovered and accessed.
How to Use the Cipher Security Tool to Overwrite Deleted Data
To overwrite deleted data on a volume by using Cipher.exe, use the /w switch with the cipher command. Use the following steps:
- Quit all programs.
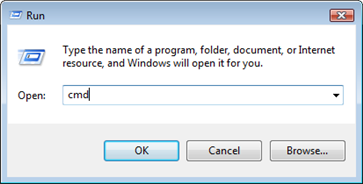
- Click Start–> click Run–> type cmd, and then press ENTER.
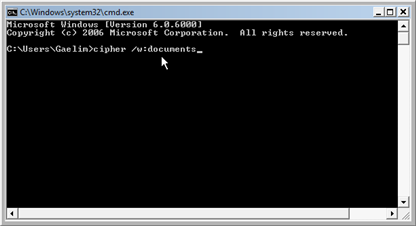
- Type: cipher /w:driveletter:foldername, and then press ENTER. Specify the drive and the folder that identifies the volume that contains the deleted data that you want to overwrite. This permanently removes the data. This can take a long time if you are overwriting a large space.
SPECIAL NOTE:
The U.S. Department of Defense endorses the secure file deletion procedure as the only method that can permanently remove data from your hard drive. This procedure can be done in minutes and with secure deletion software. However, ensure that these product can actually perform a secure delete and not simply a traditional delete.
